France’s Surveillance Bill Expands Amid Privacy Debates
French MPs vote to broaden intelligence surveillance, raising privacy concerns amidst debates on democratic oversight.

French MPs vote to broaden intelligence surveillance, raising privacy concerns amidst debates on democratic oversight.
Sweden’s open data laws clash with rising gang-related violence.

Supermarket chain’s facial recognition use in poor areas raises GDPR concerns.

The EU Parliament’s main political groups have agreed on a draft law to prevent the online spread of child sexual abuse material, focusing on detection and reporting, with provisions for encryption and age verification.

PimEyes, a public face search engine, has implemented measures to block searches of children’s faces in response to privacy concerns.
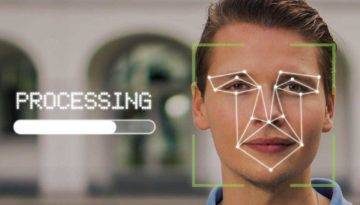
The Greek Data Protection Authority is set to decide on the legality of AI and biometric surveillance systems in the country’s refugee camps, a decision that could impact the use of such systems in migration management globally.

The Metropolitan Police Service’s Connect system encountered data protection issues and search functionality weaknesses.

The article discusses the complex legal and ethical issues arising from the creation and use of synthetic data, emphasizing the need for robust guidelines to maintain privacy and integrity while exploiting its potential benefits.

As the number of security cameras installed across the Netherlands continues to surge, concerns about their impact on public privacy are intensifying.

This report uses business consultations to investigate private-sector views on privacy and data protection rules for cross-border data flows.
Prime Minister Rishi Sunak has unveiled sweeping measures to safeguard the nation’s security.
European Parliament will vote on a proposed amendment to Article 5 of the Artificial Intelligence Act, which seeks to bar the use of live facial recognition technology on public streets.